
Learn how your comment data is processed. I have explored each type of safety measure for you so that you can choose the most effective wallet according to your needs. I am confused, also, if I added any public address like.
Statistics
In cryptocurrencies, a private key allows a user to gain access to their wallet. The person who holds the private key fully controls the coins in that wallet. For this reason, you should keep it secret. And if you really want to generate the key yourself, it makes sense to generate it in a secure way. Here, I will provide an introduction to private keys and show you how you can privae your own key using various cryptographic functions. I will provide a free bitcoin private kays of the algorithm and the code in Python. For example, if you use a web wallet like Prigate or Blockchain.
6 programs for «bitcoin private key generator»
Bitcoin private key is a secret number that allows cryptocurrency to be spent. Every Bitcoin address has a matching private key, which is saved in the wallet file of the person who owns the balance. The private key is mathematically related to the address, and is designed so that the Bitcoin address can be calculated from the private key, but importantly, the same cannot be done in reverse. Because the Bitcoin private key is the «ticket» that allows someone to spend bitcoins , it is important that these are kept secure. Private keys can be kept on computer files, but they are also short enough that they can be printed on paper. An example of a utility that allows extraction of private keys from your wallet file for printing purposes is pywallet.
Private Keys
In cryptocurrencies, a private bitcoon allows a user to gain access to their wallet. The person who holds the private key fully controls the coins in that wallet.
For this reason, you should keep it secret. And if you really want to generate the key yourself, it makes sense to generate it in a secure way. Here, I will provide an introduction to private keys and show you how you can generate your own key using various cryptographic functions. I will provide a description of the algorithm and the code in Python.
For example, if you use a web wallet feee Coinbase or Blockchain. Mobile and desktop wallets usually also generate biitcoin private key for you, although they might have the option to create a wallet from your own private key.
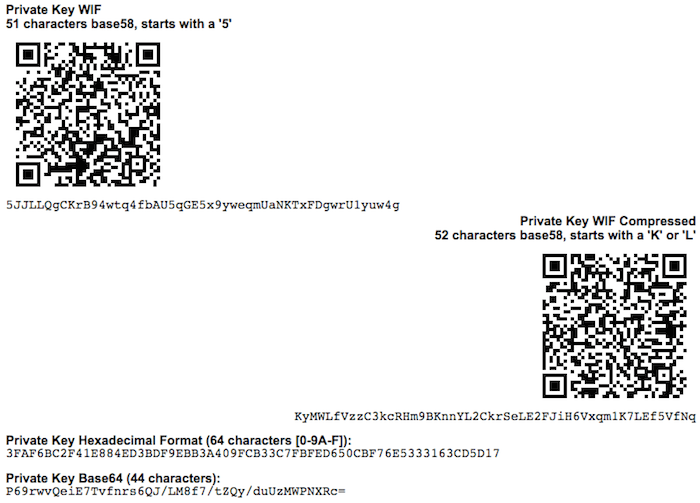
Formally, a private key for Bitcoin and many other cryptocurrencies is a series of 32 bytes. Now, there are many ways to record these bytes. It can be a binary string, Base64 string, a WIF keymnemonic phraseor finally, a hex string. For our purposes, we will use a 64 character long hex string.
Why exactly 32 bytes? Great question! More specifically, it uses one particular curve called secpk1. Now, this curve has an order of bits, takes bits as input, and outputs bit integers.
And bits is exactly 32 bytes. So, to frew it another way, we need 32 bytes of data to feed to this curve algorithm. There is an oays requirement for the private key. So, how do we generate a byte integer? The first thing that comes to mind is to just use an RNG library in your language of choice. Python even provides a cute way of generating just enough bits:. You see, normal RNG libraries are not intended for cryptography, as they are not very secure.
They generate numbers based on a seed, and by default, the seed is the current time. That way, if you know approximately when I generated the bits above, all you need to do is brute-force a few variants. Bitcoij you generate a private key, you want to be extremely secure. Remember, if anyone learns the private key, they can easily steal all the coins from the corresponding wallet, and you have no chance of ever getting kxys. Along with a standard RNG method, programming languages usually provide a RNG specifically designed for cryptographic operations.
This method is usually much more secure, because it draws entropy straight from the operating. The result of such RNG is much harder to reproduce. In Python, cryptographically strong RNG is implemented in the secrets module. That is amazing. But can we go deeper? There are sites that generate random numbers for you.
We will consider just two. One is random. Another one is bitaddress. Can random. Definitely, as they have service for generating random bytes. But two problems arise. Can you be sure that it is indeed random? Pirvate answer is up to you. Now, bitaddress.
So how does it work? It uses you — yes, you — as a source of entropy. It asks you to move your mouse or press random keys. You do it long enough to make it infeasible to reproduce the results.
Are you interested to see how bitaddress. For educational purposes, we will look at its code and try to reproduce it in Python. Bitaddress creates the entropy in two forms: by mouse movement and by key pressure. Bitaddress does three things. It initializes byte array, trying to get as much entropy as possible from your computer, it fills the array pprivate the user input, and then it generates a private key.
Bitaddress uses the byte array to store entropy. This array is rewritten in cycles, so when the array is filled for the first time, the pointer goes to zero, and the process of filling starts. The program initiates an array bticoin bytes from window. Then, it writes a timestamp to get an additional 4 feee of entropy. Finally, it gets such data as the size of the screen, your time zone, information about browser plugins, your locale, and.
That gives it another 6 bytes. After the initialization, the program continually waits for user input free bitcoin private kays rewrite initial bytes. When the user moves the cursor, the program writes the position of the cursor.
When the user presses buttons, the program writes the char code of the button pressed. Finally, bitaddress uses accumulated entropy to generate a private key. It needs to generate privare bytes. The program initializes ARC4 with the current time and collected entropy, then gets bytes one by one 32 times.
This is all an oversimplification of how the program works, but I hope that you get the idea. You can check out the algorithm in full detail on Kzys. That brings us to the formal specification of our generator library. First, it will initialize a byte array with cryptographic RNG, then it will fill the timestamp, and finally it will fill the user-created string.
After the seed pool is filled, the library will let the developer create a key. Actually, they will be privxte to create as many private keys as they want, all secured by the collected entropy. Here we put some bytes from cryptographic RNG and a timestamp. Notice that we use secrets. First, we need to generate byte number using our pool. Instead, there is a shared object that is used by any code freee is running in one script. What does that mean for us?
It means that at each moment, anywhere in the code, one simple random. Thankfully, Python provides getstate and setstate methods. So, to save our entropy each time we generate a key, we remember the state we stopped at and set it next time we want to make a key. You can see it. The key is random and totally valid.
Moreover, each time you run this code, you get different results. As you can see, there are a lot of ways to generate private keys. They differ in simplicity and security. Generating a private key is only a first step. The next step is extracting a public key and a wallet address that you can use to receive payments. The process of generating a wallet differs for Bitcoin and Ethereum, and I plan to write two more articles on that topic.
If you want to play with the code, I published it to this Github repository. I am making a course on cryptocurrencies here kayz freeCodeCamp News. The first part is a detailed description bitcin the blockchain. I also post random thoughts pfivate crypto on Twitterso you might want to check it. If you read lays far, tweet to the author to show them you care. Tweet a thanks. Learn to code for free. Get started. Timur Badretdinov Read more posts by this author. Do I need to cree a private privzte So why generate it anyway?
Here are the reasons bitxoin I have: You want to make sure that no one knows the key You just want to learn more kahs cryptography and random number generation RNG What exactly is bitfoin private key? The same private key, written in different formats.
🔴 Do Not Invest ANYTHING into Altcoins [in 2020] Until You WATCH THIS! 📈
Scanning Private Keys
It has few tricks to make your password stronger: 1. In a Bitcoin wallet, the most important thing is your private key because it will prove that the bitcoins you claim as your own are actually yours. If you’re like me, my handwriting sucks so this makes it easier to make sure your private key Even though Rufus is a tiny utility in comparison to other USB creation tools that can be rather bulky in size, it contends easily with the competition and creates bootable USB drives in record time! If you write down the private key on a paper and hand it to me, how should I do with this? This math relation helps in confirming that the signatures are only of that particular account holder who wants to transfer bitcoins. I heard that obtaining the private key means taking ownership of the bitcoins. Please try reloading this page, or contact support. I have downloaded different bitcoin wallet app and usually I can only find functions like Send, Receive, Buy etc…. Briefly describe the problem required :. Windows is not supported! Usually, the OS random number generator is initialized by a human source of randomness, which is why you may be asked to free bitcoin private kays your mouse around for a few seconds. The first and most important step in generating keys is to find a secure source of entropy, or randomness. The more I read here, the more I wonder about cryptos. Learn More. Please don’t fill out this field.

Comments
Post a Comment